Last Updated on 5 days by Sachin G
Linux systems are widely considered secure, but even the most robust system can become vulnerable if permissions are misconfigured. Among the most critical aspects of Linux security are special permissions, which include SUID (Set User ID), SGID (Set Group ID), and the Sticky Bit. These permissions were designed for specific functionality but can also open doors for hackers to exploit privilege escalation vulnerabilities.
In this article, you’ll learn:
✔ What special permissions are
✔ Why they can be dangerous
✔ How to identify and remove them
✔ Best practices for hardening your Linux system
By the end, you’ll have the knowledge and commands to secure your Linux environment effectively.
1. Understanding Linux Special Permissions
Linux has three basic permissions for files and directories:
- Read (r) – View content
- Write (w) – Modify content
- Execute (x) – Run as a program
However, special permissions go beyond these:
SUID (Set User ID)
- Purpose: Allows users to execute a file as the file’s owner.
- Example:
/usr/bin/passwduses SUID to let users change passwords. - Risk: If a hacker finds a vulnerable SUID binary, they can gain root access.
SGID (Set Group ID)
- Purpose: Similar to SUID, but applies to group permissions.
- Risk: Could allow unauthorized group-level access.
Sticky Bit
- Purpose: Prevents users from deleting files they don’t own in shared directories like
/tmp. - Risk: Generally safe when used correctly, but misconfigurations can lead to issues.
Special permission can be useful in some scenarios, but it can also pose security risks if not managed properly. Intruders often target files with special permissions to execute malicious code and escalate their privileges on the system. In Linux systems, special permissions are suid, sgid, and a sticky bit to give additional privileges to users and processes.
The “suid” permission, also known as the Set User ID, grants users the ability to execute a file with the permissions of the file owner, regardless of who is running it. On the other hand, the “sgid” permission, or Set Group ID, enables files and directories to inherit the group ownership of their parent directory, ensuring consistent group ownership throughout the directory structure.
Why Hackers Exploit SUID and SGID
Files with SUID or SGID can execute with elevated privileges. Attackers search for these files using commands like find and then leverage known vulnerabilities to execute malicious commands as root.
Example of an SUID file:
-rwsr-xr-x 1 root root /usr/bin/passwdThe ‘s’ in rws indicates SUID.
How to Identify Files with Special Permissions
First, we should know which files are critical and contain sensitive data for the system operation. This can be system configuration files, system binaries, and files containing user credentials or sensitive information. Mostly binary and configuration on /usr/bin /usr/sbin and /etc folder. Let’s look at how we can find files that have SUID and SGID through the find command. Read about the find command, Just Read it Find command.
To find files with SUID, SGID, and Sticky Bit:
The below find command syntax according to permission is
find search_directory -perm /permission
# Find all SUID files
find / -perm /4000 2>/dev/null
# Find all SGID files
find / -perm /2000 2>/dev/null
# Find all Sticky Bit directories
find / -perm /1000 2>/dev/null
Tip: Use
sudoif necessary for system-wide scans.
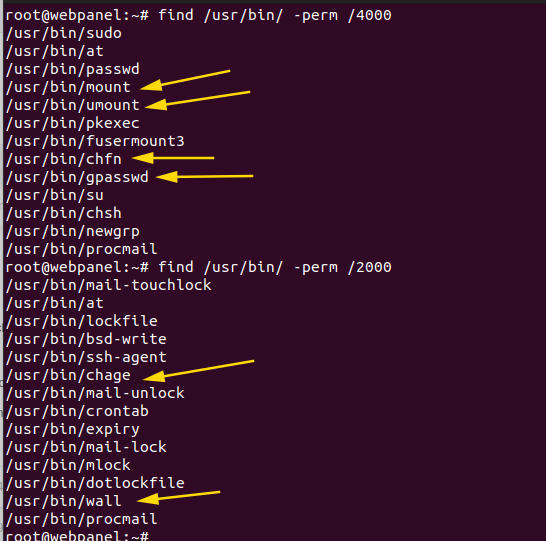
In my case, I scanned the /usr/bin directory for files with SUID and SGID permissions. The search returned many files, including critical ones such as chage, gpasswd, wall, chfn, chsh, newgrp, mount, and umount. These files are essential for system operations, so we should avoid removing special permissions from them.
How to Remove special permissions of important files in Linux
To remove special permissions of an important file in Linux, you can use the chmod command followed by the appropriate flags. For example, to remove the suid permission from a file, use the command chmod u-s filename. Similarly, to remove the sgid permission, use chmod g-s filename. For files with the sticky bit set, use chmod o-t filename.
chmod u-s/g-s [filename]
The screenshot below shows, I removed some special permissions on selected files. You should be an expert in Linux to identify which files you should remove with special permissions.

Be careful when changing permissions. Incorrect changes could affect system functionality. Research specific file permissions before making changes.
Automating Permission Cleanup
To remove SUID from all files in /usr/bin:
find /usr/bin -perm /4000 -exec chmod u-s {} \;To remove SGID:
find /usr/bin -perm /2000 -exec chmod g-s {} \;Warning: Do not remove SUID from essential system files like
/usr/bin/passwdor you may break system functionality.
Hardening Tips Against Hackers
- Regularly audit SUID and SGID files.
- Use tools like Lynis or chkrootkit to detect vulnerabilities.
- Restrict access to critical directories.
- Apply security patches and keep binaries updated.
FAQs
No. Some are required for normal system operations. Audit and remove only unnecessary ones.
Hackers can exploit them for privilege escalation and take full control of your system.
Removing unnecessary special permissions like SUID, SGID, and Sticky Bit is an important step in Linux system hardening. By auditing your files and applying the commands above, you significantly reduce the risk of privilege escalation and hacking attempts.
Learn Smarter. Level Up Faster →
Want to master Linux, DevOps, Ansible, or Cloud workflows the smart way? I’ve curated a list of top-rated, real-world Udemy courses — based on student reviews and practical feedback.
Visit the Recommended Courses page to explore and enroll in courses trusted by the community.
See Curated Courses →
I’m Sachin Gupta — a freelance IT support specialist and founder of techtransit.org. I’m certified in Linux, Ansible, OpenShift (Red Hat), cPanel, and ITIL, with over 15 years of hands-on experience. I create beginner-friendly Linux tutorials, help with Ansible automation, and offer IT support on platforms like Upwork, Freelancer, and PeoplePerHour. Follow Tech Transit for practical tips, hosting guides, and real-world Linux expertise!
